Key Advantages of Managed eXtended Detection & Response (MXDR)
Indeed, the most glaring issue in cybersecurity today is a lack of skills within organizations....
Platform for Cyber Analytic & Hybrid SecOps
Data Protection ▼Secure Your Data From Potential Threats
High Speed Cyber Defense to Thwart Threats in Real Time
Service Comparison ▼See How MXDR Compares to Other Platforms
Our experts weigh in on the cybersecurity landscape
What Superintendents Need to Know ▼Protect Your School District, Your Students, and Your Staff With Highly Specialized K-12 Cybersecurity
Our insights into complex cybersecurity challenges
Ransomware Calculator ▼How Much Could a Ransomware Attack Cost Your Business?
14 years of experience in Data Protection, Cybersecurity & Compliance.
Blind Spot ▼Short video on the problem we solve
Managed eXtended Detection & Response (MXDR) is a new, evolving genre of cybersecurity defense, providing a platform for outsourcing cybersecurity functions and services to protect your IT infrastructure and data. MXDR is a recommended alternative for identifying and responding to never-before-seen attacks and the most elusive cyber threats that are virtually undetectable by standard on-premises cybersecurity controls.
Cyber threats continue to evolve and increase in both frequency and sophistication, while many companies struggle to maintain well-equipped security operations centers (SOCs) staffed with competent cybersecurity professionals. A recent Devo SOC Performance Report revealed that 40 percent of organizations struggle with SOC staff shortages. Moreover, 78 percent of in-house security personnel find it very painful to work in a SOC due to stress-related burnout. Experts estimate that this problem will continue to grow, with cybercrime estimated to have cost the world $6 trillion in 2021 and expected to increase by $10.5 trillion annually thru 2025.
Many organizations can enhance their effectiveness by outsourcing essential cybersecurity services to MXDR vendors. MXDR platforms facilitate advanced protection and response, analytics and automation while leveraging Artificial Intelligence (AI) and Machine Learning (ML). These functions enable the anticipation, detection and identification of threats within business-generated data. The best providers of MXDR services integrate sophisticated technology with skilled, human cybersecurity analysts to address and respond to cyber threats. In this way, the protection of data and infrastructure from complex assaults by unknown attackers is hardened.
The need to develop MXDR solutions is necessitated by three primary trends emerging within the IT landscape.
Organizations across all industries are embracing new technological tools and solutions faster than ever before. This digital transformation has encouraged businesses and enterprises to invest in endpoint controls and devices. The objective of this investment is to increase productivity and output. However, this business strategy has a shortcoming in that it expands the attack surface available to malicious actors. The phenomenon leaves organizations highly vulnerable to numerous cybersecurity threats. Enterprises remain increasingly exposed as they lack the necessary talent, skills and tools to detect and respond to incoming as well as already embedded bad actors and malware.
Building next-generation capabilities for threat detection and response is not feasible for many organizations due to the expense involved and the lack of cybersecurity talent available today. Securus360 MXDR services solve this challenge by delivering advanced detection and response capabilities as a service, thereby removing the complexity and cost of building an in-house, next-generation security operations center.
Securus360 MXDR helps anticipate and hunt for cyber threats beyond passive security monitoring. An alert must pass a 21-point checklist to be validated before it is sent to a client; we can also deliver enhanced threat containment of identified threats and assist with incident response. We follow distinct phases of threat management and provide an AI-driven MXDR service for each phase. Our MXDR platform coordinates appropriate actions during each phase of the threat’s lifecycle, helping our customers achieve tangible and measurable high-speed cyber defense.
Key phases of the process include:
From security news to protection within hours.
Our platform applies global threat intelligence for enhanced protection. Every day you read or hear about a new security threat that has claimed multiple victims. After an initial success, attackers typically repeat their attack against other targets across industries and geographies. A vital part of the MXDR service from Securus360 is to gather data and intelligence on known threats and attacks worldwide,distill this information to identify which customers might be affected, then detail each customer's specific actions to protect their digital assets before such an attack can be launched. This tailored threat anticipation goes far beyond traditional passive threat intelligence feeds that are available. Instead of the days or weeks traditionally needed to move from news to protection, Securus360 can make it happen within hours, or even minutes.
We continuously collect threat data from various feeds, news, blogs, social media and dark web resources in the platform’s proprietary threat intelligence module. The data is analyzed in each organization and vertical market to determine the possibility for threats to materialize. If a threat is likely to occur, measures are put into place for detecting it quickly and responding immediately with appropriate response playbooks.
Do not wait for the bad guys to show up on the radar, hunt them!
We apply data science and machine learning models to network, user, and machine data to proactively hunt for unknown and hidden threats within your environment. Our platform uses data science models and machine learning algorithms to detect suspicious and irregular activities. A specialized hunting team then analyzes these outputs and queries the data further to detect serious threats that may have bypassed other security controls.
Utilizing our integrated Security Information and Event Management (SIEM), we apply real-time rules to logs and security events to detect attacks. A variety of SIEM technologies are available to organizations, but they can be hard to operationalize and maintain in-house. Our MXDR offering delivers the SIEM outcome for detecting threats, policy, and compliance violations. We also leverage existing SIEM investments by our clients, integrating their logs to provide enhanced visibility to threats.
We collect client logs and security events for analysis on our big data SIEM platform. Instead of a static approach, we build and constantly fine-tune the rules for detecting threats and instances of non-compliance. We then monitor the alerts on a 24x7 basis and notify the client according to the severity of these alerts after our in-house cybersecurity analyst team has thoroughly vetted them.
We extend security monitoring to hybrid and pure cloud infrastructures. Connectors along with specific use cases enable detection of attacks to cloud consoles, including Azure and AWS. 24x7 monitoring also enables the protection of the cloud infrastructure for all types of deployments, including PaaS and SaaS. Deep connectors and specialized use cases enable the detection of new age attacks on cloud applications. Comprehensive coverage is provided for AWS, Azure, Office 365 and its components, including email, DLP, SharePoint, Intune, and Dynamics.
Not every alert is an incident, and not every incident is an alert.
Triaging the alerts to focus on the most relevant threats and then investigating them to establish a security incident is critical. The Securus360 platform converts alerts into more meaningful information such as the attack chain, blast radius, and potential impact on assets.
Not every alert needs an incident response plan to be activated. The alerts need to be investigated for who, what, when and how to determine the impact's extent. Our MXDR offering validates the threats with AI and human intelligence to provide the most profound incident analysis available on the market today.
Activate orchestrated remediation in minutes to contain incidents.
Execution of rapid, coordinated activities for containment, eradication, and recovery is a critical aspect of cybersecurity. Threat containment technologies have emerged for automating incident response, but they need organizations to build up a considerable knowledgebase and hire the requisite skills to utilize them. As a practical alternative, our MXDR offering provides threat containment as a service in a collaborative approach between the organization’s team and our specialized responders via our response orchestration technology platform.
We use our response automation platform with its response workflows, case management, forensic tools and playbooks for various incidents. Our responders collaborate with an organization’s distributed teams to contain, mitigate and recover from significant incidents leveraging our platform and our knowledgebase. Our teams also build and update response playbooks as new incidents emerge to ensure our clients have everything they need to respond to a bona fide incidence of compromise.
Get back to business operations fast!
When there is a breach of protected data (PCI, HIPAA, PII, etc.) or confidential customer data, our MXDR service assists in incident response. We provide services for forensics, evidence collection and retention, assessing the impact on compliance with regulatory requirements, and best practices for breach notifications.
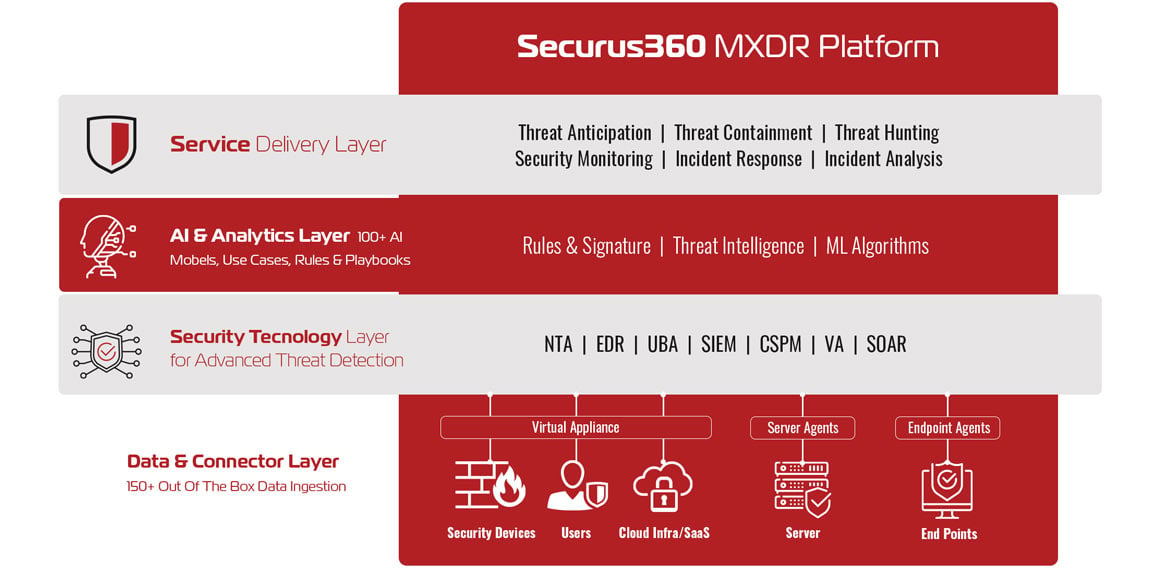
As discussed above, Securus360 MXDR platform combines multiple cybersecurity activities, such as threat intelligence, advanced analytics, threat containment, threat hunting, threat anticipation and 24/7 security monitoring. The system has sophisticated Artificial Intelligence and Machine Learning models woven throughout.
Delivering all the details on one pane of glass, the Securus360 MXDR platform comes as a complete service ready to deploy while leveraging the client’s existing security solutions. With our highly qualified analysts and cybersecurity experts who are constantly monitoring events and on standby to respond to any cyber incident, we complement a client’ current security personnel as an extension of the team with enhanced Always-On 24x7 protection.
Contact Us to Learn More!
Indeed, the most glaring issue in cybersecurity today is a lack of skills within organizations....
Does your current cybersecurity posture...
Copyright © 2025 Securus360 | Privacy Policy | Cookie Policy | Terms and Conditions | Disclaimer